I've decided to try and build a virtualized workstation that would allow me to use multiple OSes on top of my Mac Pro. That's no piece of cake, because it mainly boils down to using a professional hypervisor optimized for hardware abstraction and headless operation as a power-user workstation with full hardware access and as much GPU power as possible. It does not look like something that has a bright future, does it?
After some experiment I have a pretty good idea of what is possible and what is not possible. Lets compare the Mac Pro's hardware and what you can access from within a virtual machine running in ESXi on the same Mac Pro:
| Mac Pro | VM | |
|---|---|---|
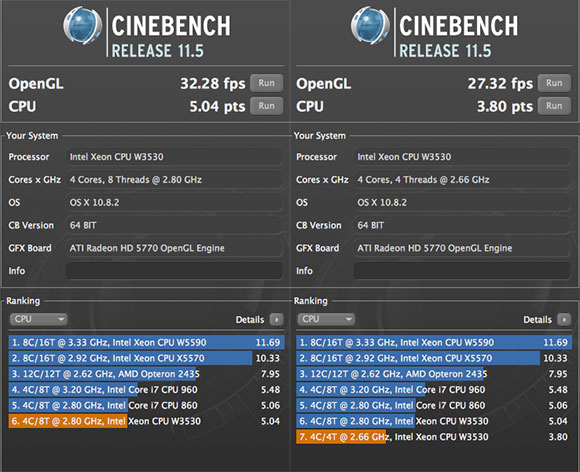
| CPU | Full power with HT | No HT, number of cores depends on the VM setup, but frequency can be lower than expected. Running OS X 10.8 I got 2.66 GHz in the VM despite the 2.8 GHz Xeon |
| RAM | Full RAM | Depends on the VM setup, but if you use device passthrough, you must reserve the full amount of RAM, meaning you lose the ability to share unused RAM with other VMs. If you are a virtualization expert you know it's not good. |
| SATA | Full access | Possibility of raw device mapping |
| USB | Full access, plug & play | Passthrough available but limited: no keyboard and no mouse. Probably no plug & play either. Tested with logitech headphones: flaky sound with kernel log message complaining about a problem in USB driver, any app (itunes, chrome...) won't play sound any longer than 2 or 3 seconds before shutting down the sound output. |
| Bluetooth | Full access | |
| Wifi | Full access | Passthrough possible, but not tested |
| LAN | Full access | Passthrough possible, not tested. Otherwise access via the virtual network stack of the hypervisor, works well. |
| Firewire | Full access, plug & play | none. |
| Graphics card | Full access | Passthrough possible, with a performance drop. Some softwares will just not work, see last part of this post for details. |
| DVD | Full access | Passthrough possible, not tested. Access via VCenter possible. |
| Optical sound output | Full access |
This chart means important things. Running a virtualized Mac OS X workstation on top of ESXi will prevent me from:
- using 100% CPU power (not that important)
- using 100% of my RAM (not that important)
- using 100% of my already limited GPU power (kind of important)
- plug in USB devices like thumbdrives (important)
- plug in Firewire devices like my CF-card reader (important)
- accessing bluetooth device (I don't care)
- using my optical Edirol MA-15D or any other good speaker (important)
Lets face it, those limitations alone could bring my project to a halt. I don't want a crappy workstation, and if virtualization is not the way to go, I might go the other way around and buy a small PC for every other OS I want to run. Even if it defeats the all-in-one purpose of the virtualization, it would allow me full access to each hardware resources.
Below, the "About this Mac" dialog featuring the VM on top and the real Mac Pro under.
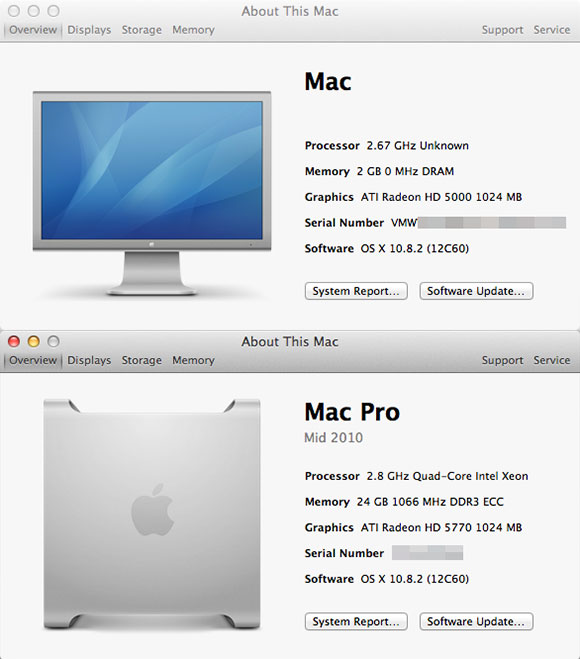
Even simple hardware features are not well recognized, but it's enough for the average user experience. The GPU passthrough allows decent full screen 1080p HD video playback from youtube, and many games should work too. Unfortunately Valve's games won't work (Left 4 Dead…) as they make use of some framework that fails on Virtualized hardware.
hl2_osx[772]: -[__NSCFString bytes]: unrecognized selector sent to instance 0x2827350 hl2_osx[772]: An uncaught exception was raised hl2_osx[772]: -[__NSCFString bytes]: unrecognized selector sent to instance 0x2827350 hl2_osx[772]: ( 0 CoreFoundation 0x988b212b __raiseError + 219 1 libobjc.A.dylib 0x9545352e objc_exception_throw + 230 2 CoreFoundation 0x988b5d9d -[NSObject(NSObject) doesNotRecognizeSelector:] + 253 3 CoreFoundation 0x987fe437 ___forwarding___ + 487 4 CoreFoundation 0x987fe1e2 _CF_forwarding_prep_0 + 50 5 CoreFoundation 0x9878d720 CFDataGetBytePtr + 80 6 launcher.dylib 0x0041c955 _ZN12GLMDisplayDB17PopulateRenderersEv + 2005 7 launcher.dylib 0x00418607 _ZN12GLMDisplayDB8PopulateEv + 23 8 launcher.dylib 0x0041b18f _ZN9CCocoaMgr12GetDisplayDBEv + 159 9 shaderapidx9.dylib 0x0b28fb47 _ZN10IDirect3D921GetAdapterDisplayModeEjP15_D3DDISPLAYMODE + 55 10 shaderapidx9.dylib 0x0b2db946 _ZNK19CShaderDeviceMgrDx818GetCurrentModeInfoEP19ShaderDisplayMode_ti + 38 11 engine.dylib 0x05dbdeaa _Z14Shader_Connectb + 122 12 engine.dylib 0x05f1232a _ZN10CEngineAPI7ConnectEPFPvPKcPiE + 106 13 launcher.dylib 0x004151c3 _ZN15CAppSystemGroup9OnStartupEv + 115 14 launcher.dylib 0x00415575 _ZN15CAppSystemGroup3RunEv + 37 15 launcher.dylib 0x00415598 _ZN15CAppSystemGroup3RunEv + 72 16 launcher.dylib 0x0041d202 _Z18MainFunctionThreadPv + 82 17 launcher.dylib 0x0041d56c ValveCocoaMain + 140 18 launcher.dylib 0x0040ca61 LauncherMain + 673 19 hl2_osx 0x00001d26 start + 54 )
I've discovered that the [__NSCFString bytes]: unrecognized selector sent to instance error affects also Hackintosh users, ie. people running Mac OS X on top of non-Apple hardware.
Next step: try Valves games on the Windows VM, with GPU passthrough.